CrowdStrike Falcon® ASPM
Manage risk, not vulnerabilities
Prioritize and mitigate cloud threats with unmatched application visibility and business context.
Know your application security posture: any application, any cloud
The Falcon ASPM approach
Customer assessment
95%
reduction in vulnerability noise. Move from focusing on thousands of vulnerabilities to the few with the most impact on your business.
Customer assessment
20 mins
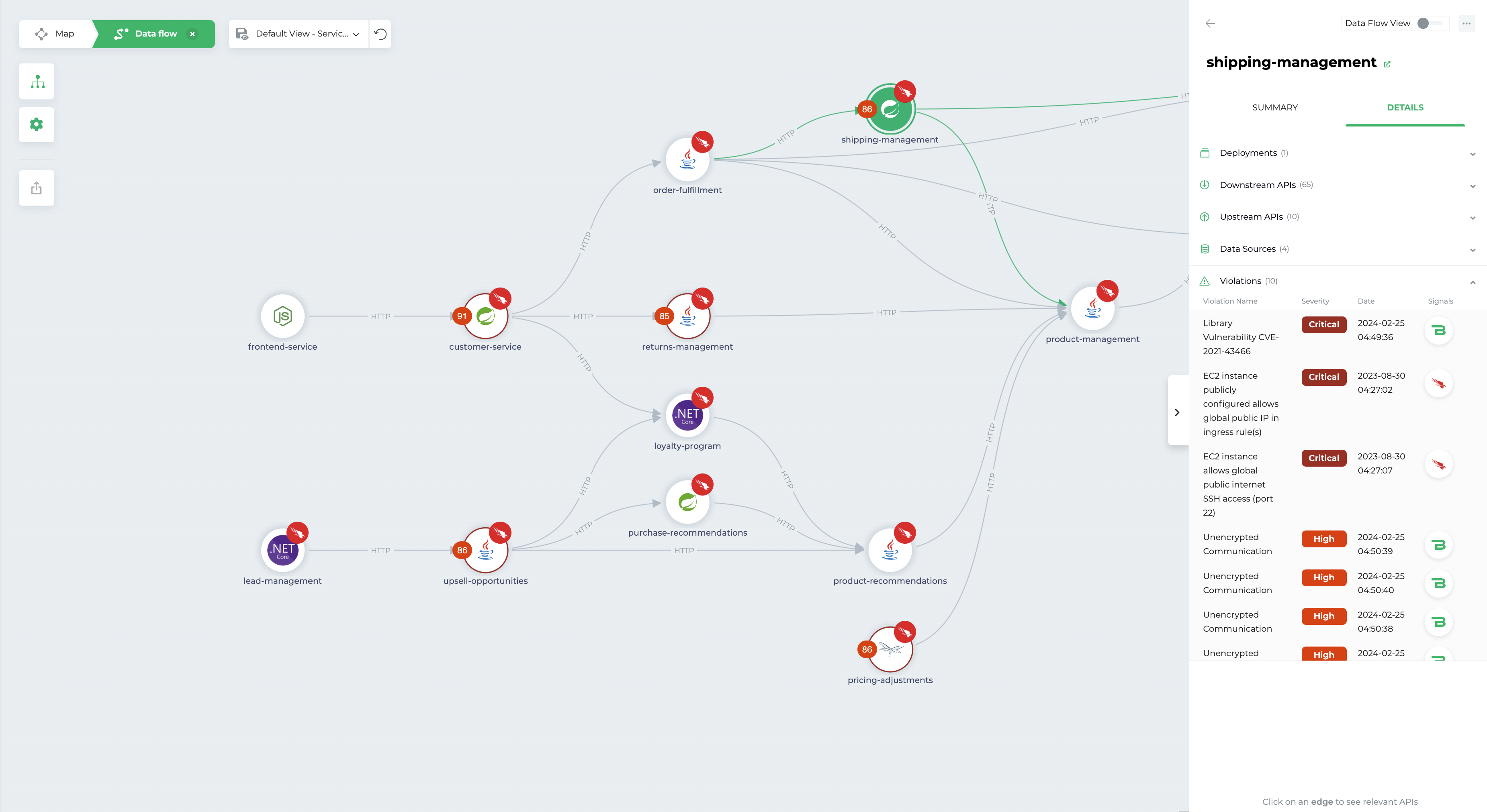
to map an application, not months. See everything—applications, microservices, APIs, data flows, and all dependencies—without the pain of outdated docs or diagram.
Customer assessment
25%
improvement in productivity across development and security teams. Accelerate DevSecOps with a common language everyone understands.1
Royal Caribbean secures their applications with CrowdStrike
The pioneer of ASPM
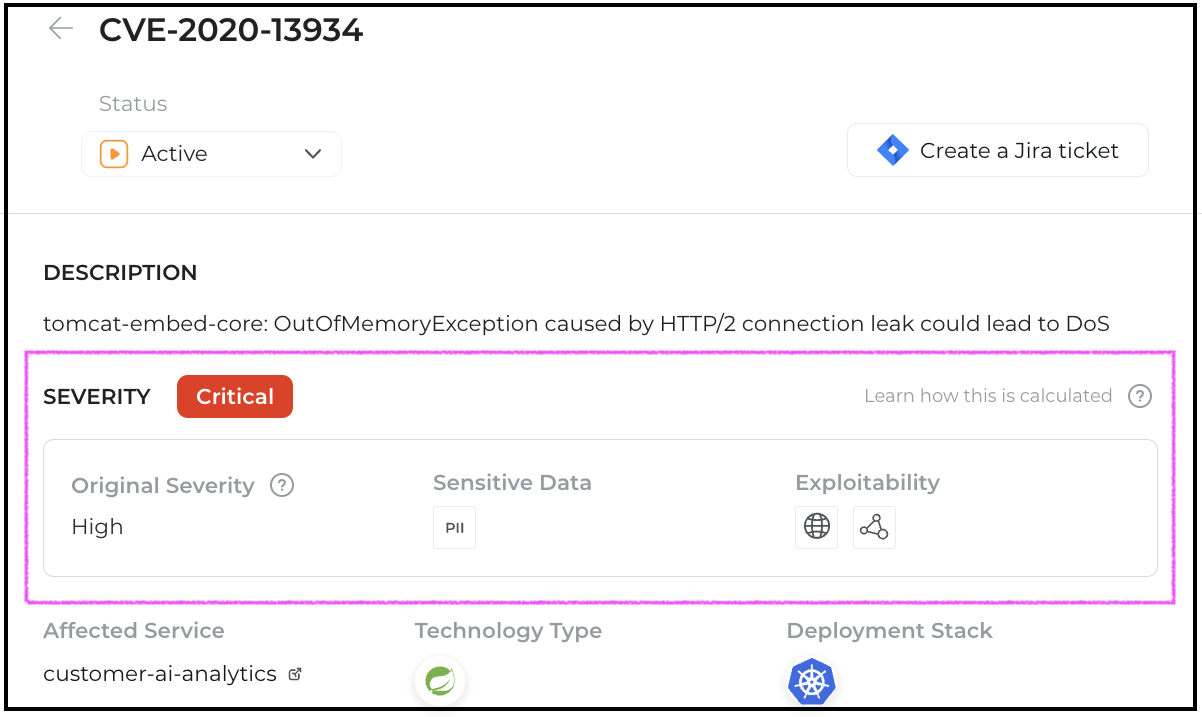
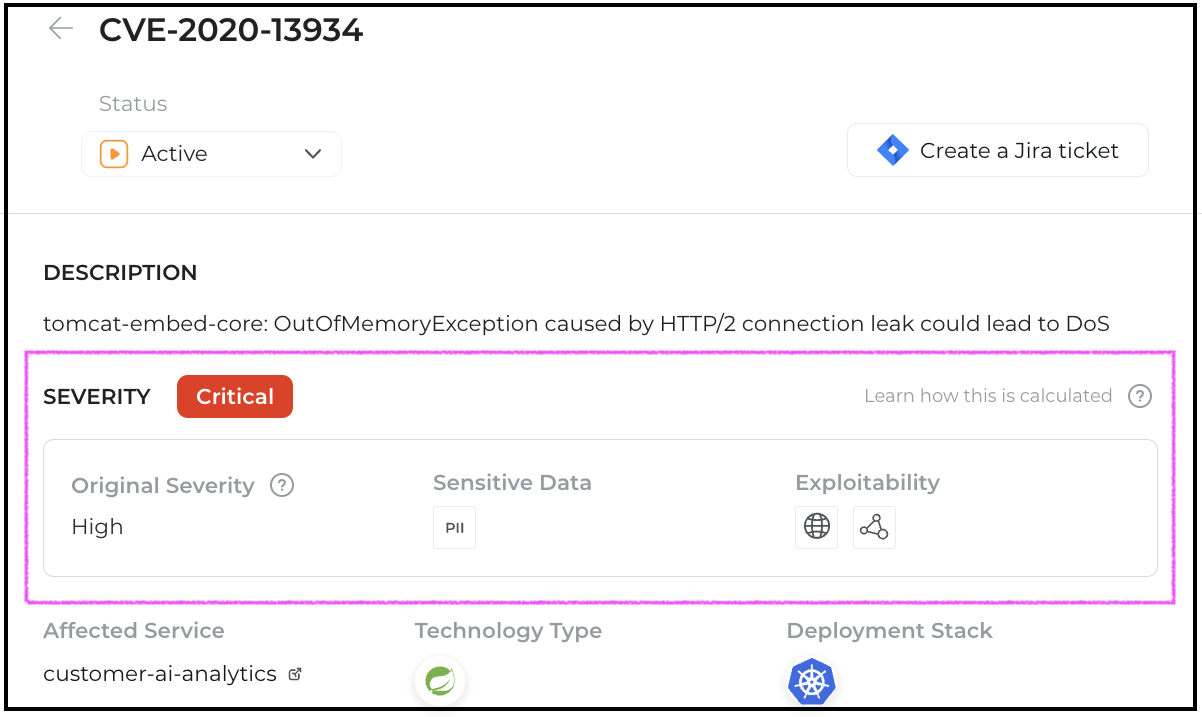
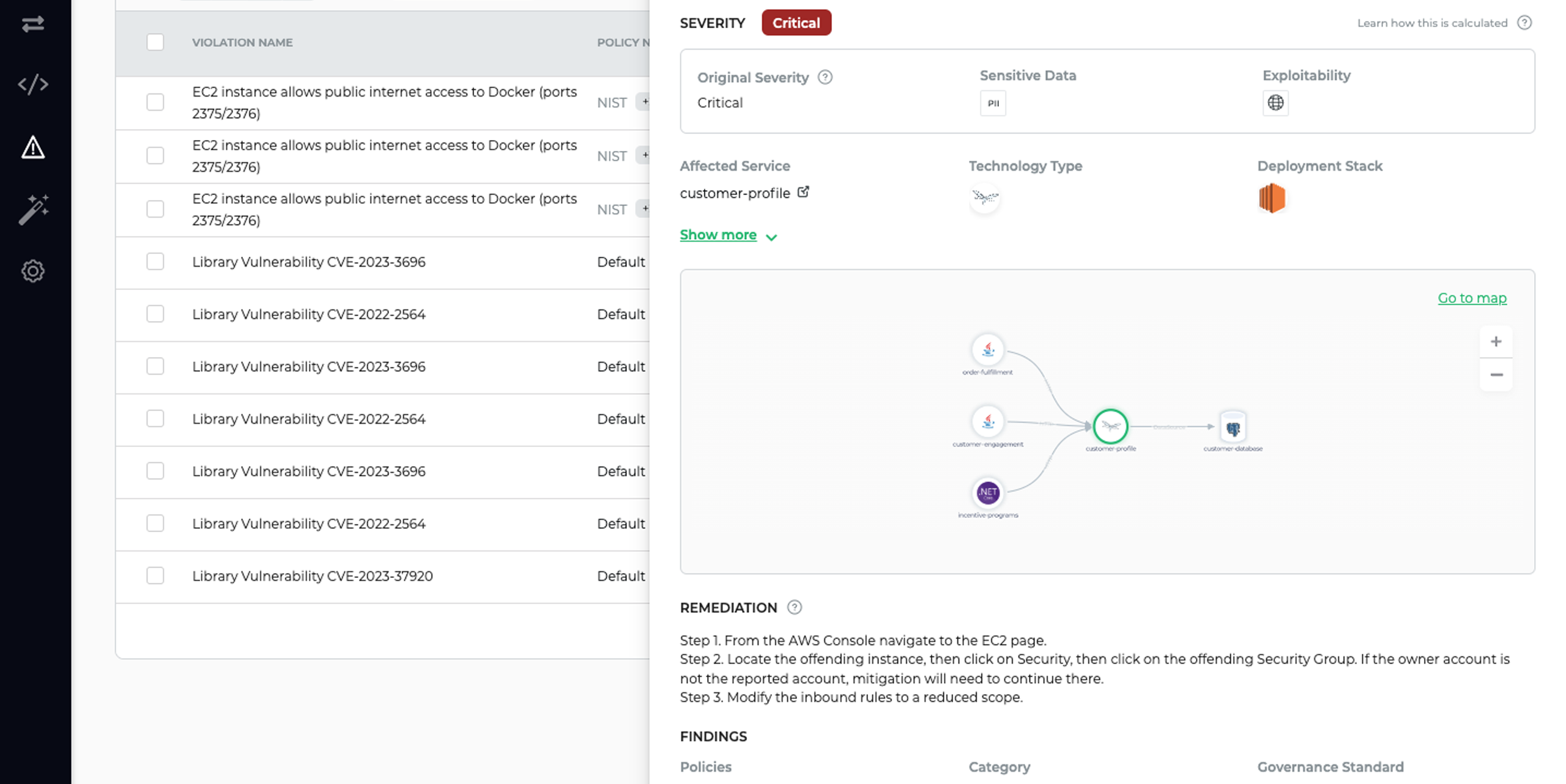
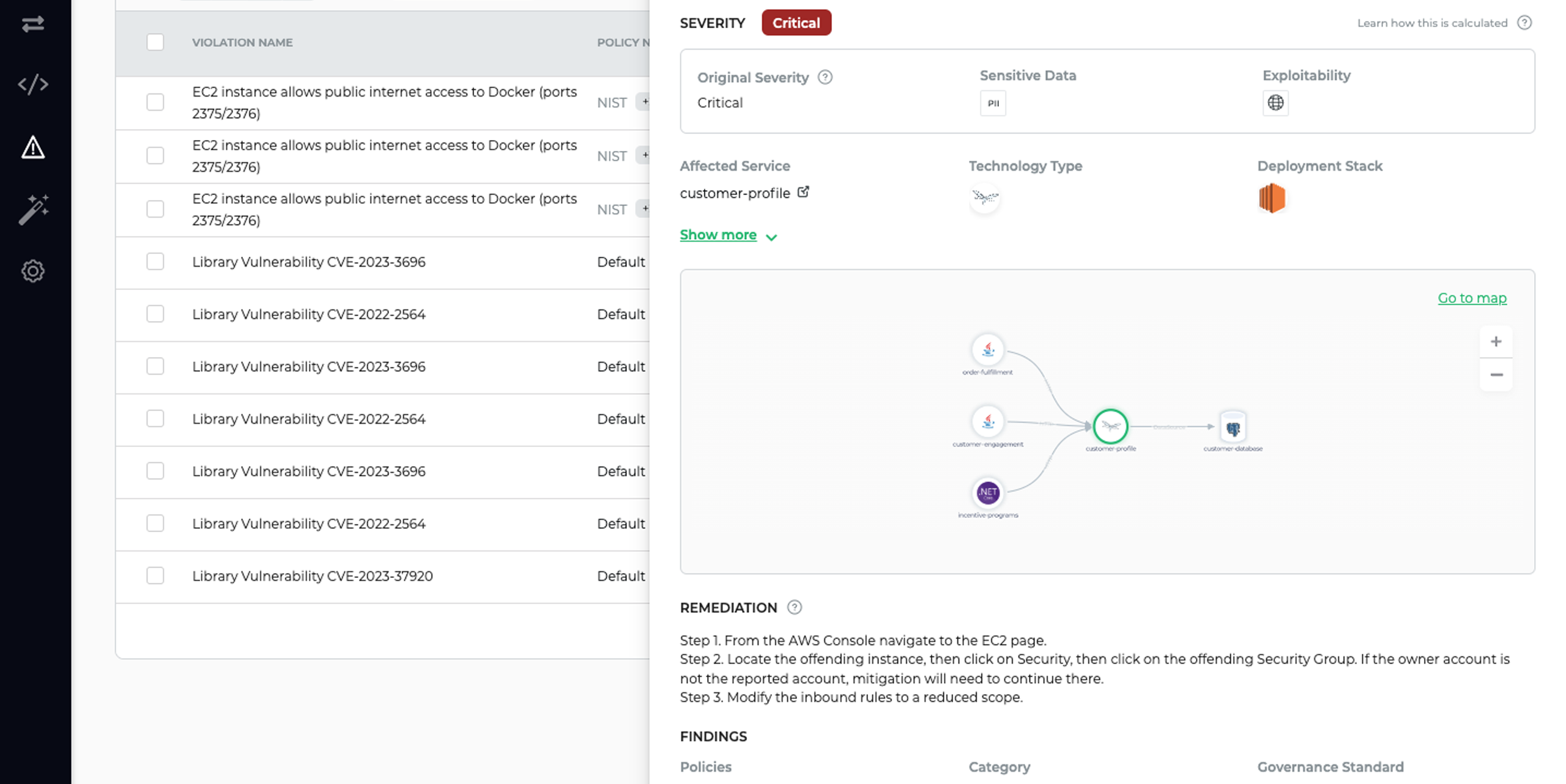
Falcon ASPM is fundamentally different from any other application security solution on the market. By mapping out your deployed applications, layering in context and assessing risk based on impact, likelihood and exploitability, you’ll get a clear and prioritized list of your top risks.
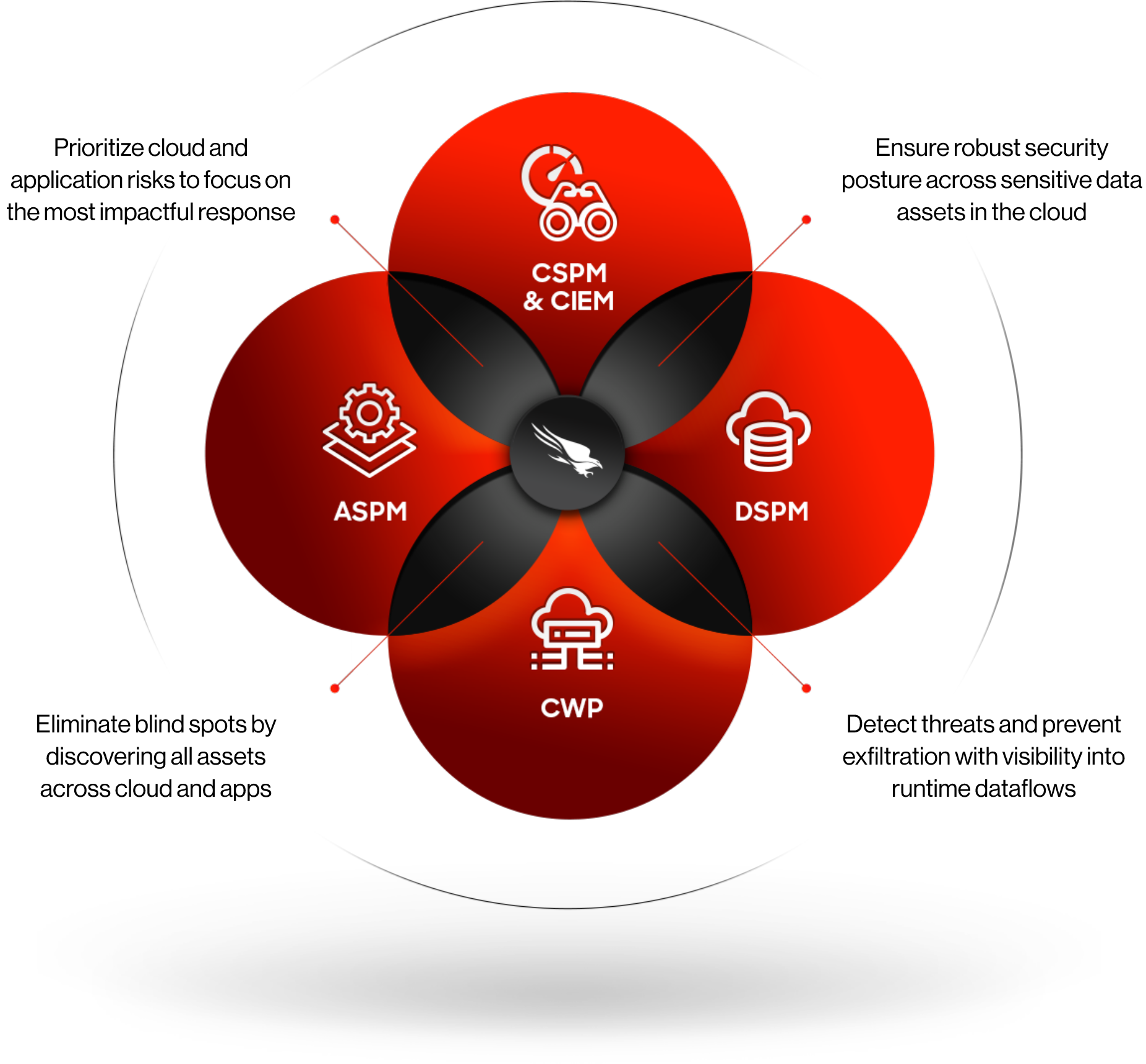
Key capabilities of Falcon ASPM
See it all
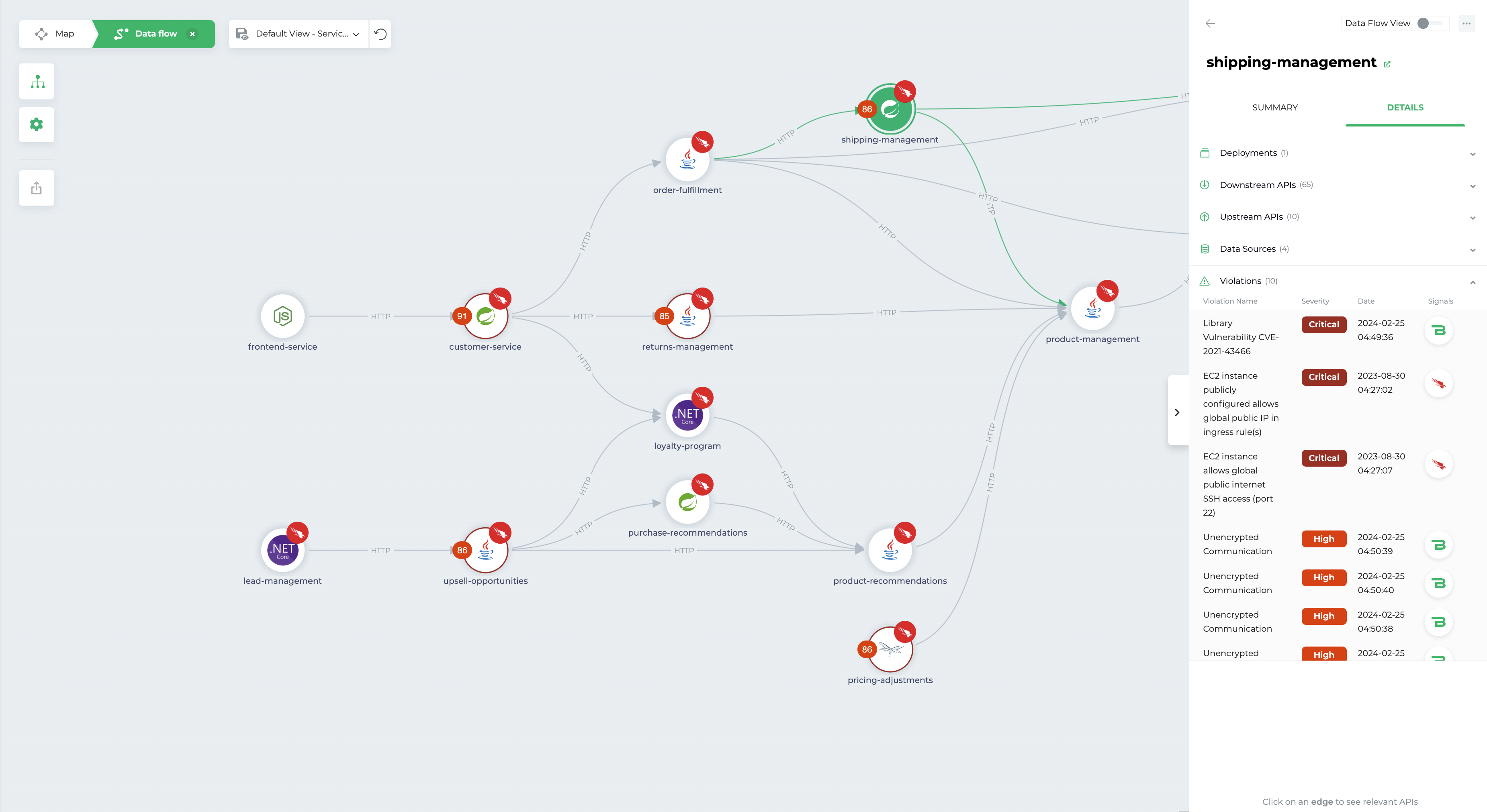
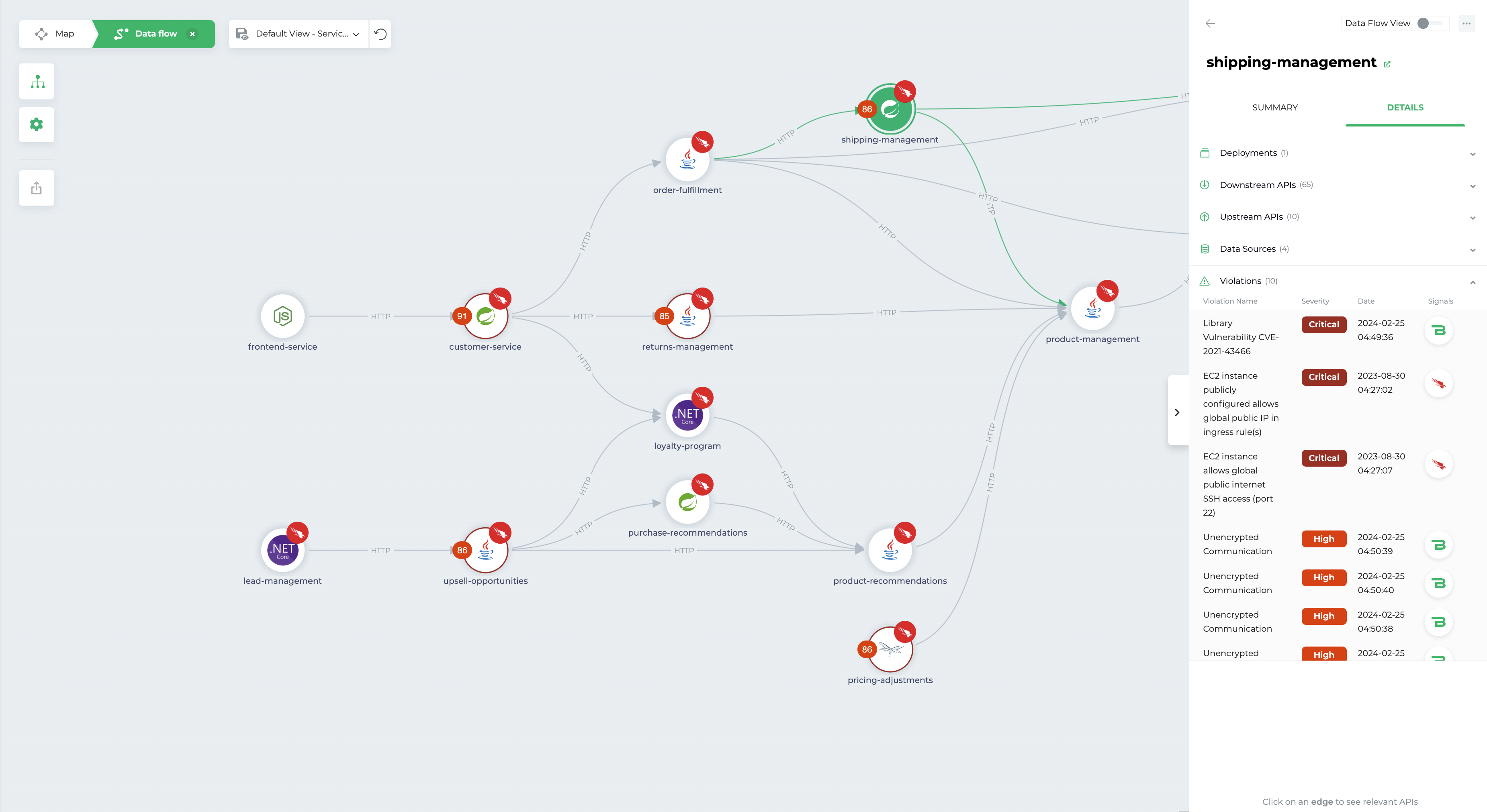
Agentless application mapping
Get a code-accurate map of your applications in production, including every microservice, database, API and dependency.
Enrich your CMDB with accurate application inventories and generate up-to-date SBOMs on demand.
Deploy in seconds with zero impact on performance.
Prioritize top risks
See your security landscape through the lens of business priorities by correlating cloud risks to apps and microservices. Know the real-world implications of each threat, helping you understand where to focus your defense.
Automatically track and secure critical data flows in your production, spotlighting and protecting data that could be exploited — PII, PCI, and PHI, we’ve got it covered.
Automate DevSecOps workflows
Fix the top risks to your deployed applications quickly by providing developers with the exact location of the issue and clear remediation steps.
Automate incident management workflows across security, DevOps, and engineering teams with integrations for Jira, Azure DevOps, and ServiceNow.
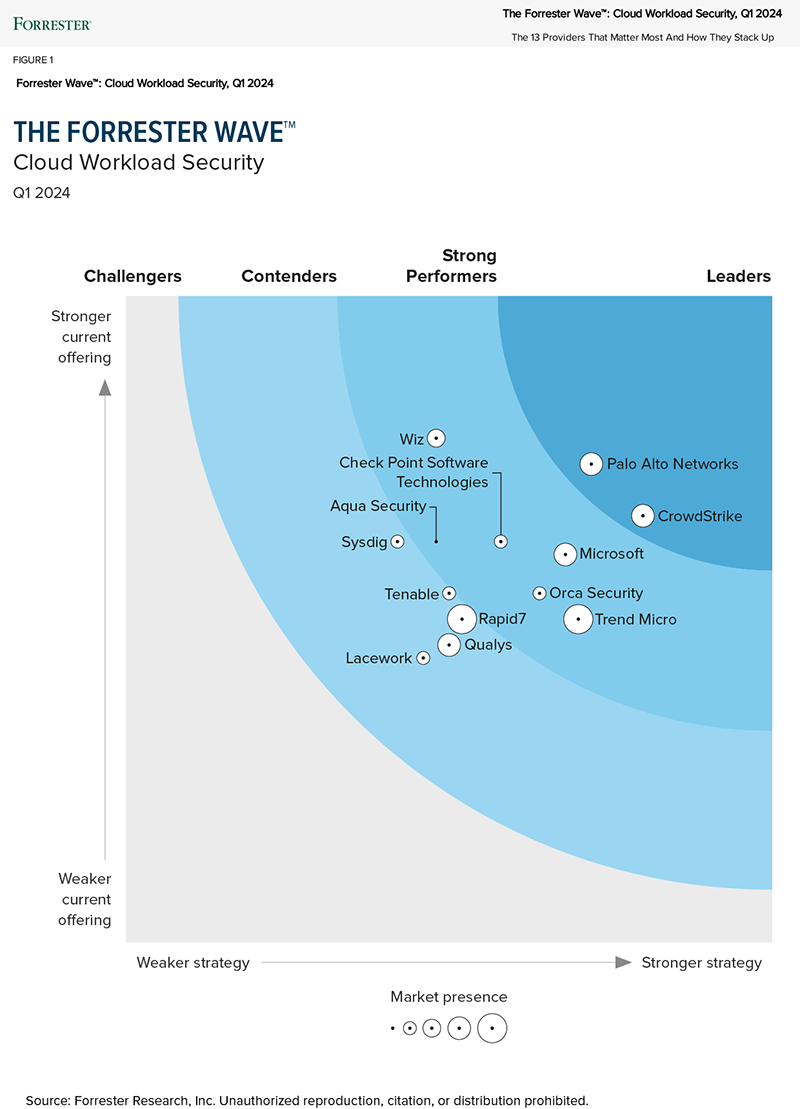
Forrester names CrowdStrike a “Leader” in The Forrester Wave™: Cloud Workload Security, Q1 2024
CrowdStrike receives the highest score of all vendors in the Strategy category and receives the highest scores possible in the Vision and Innovation criteria.
See the power of Falcon Cloud Security in under three minutes

Is your cloud secure?
Evaluate your cloud security for free with a quick, agentless health check. No strings, no hassle.
Schedule free assessmentFeatured resources
1 These numbers are projected estimates of average benefit based on recorded metrics provided by customers and prospects during pre- and post-sales motions. Actual realized value will vary .